Red Teaming vs. Pen Testing: Key Differences and How to Choose the Right One
Explore key differences between pen testing and red teaming to boost security and reduce risks.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
Penetration testing and red team assessments are two powerful cybersecurity evaluation tools. Though often confused, they serve very different purposes. Understanding these distinctions is crucial for any organisation looking to improve its red team cyber security posture.
In this article, we'll break down the core differences between red penetration testing and red teaming, explain what each involves, and help you determine which one best aligns with your goals and resources.
What is Penetration Testing?
Penetration testing (or pen testing) is a simulated cyberattack conducted with your organisation’s full awareness and cooperation. The goal is to uncover and exploit vulnerabilities in a specific system, application, or network—before real attackers can do so.
During a red penetration testing engagement:
The scope is clearly defined (e.g., an internal network, API, or web application).
Certain technical controls may be relaxed (like web application firewalls) to allow efficient testing within a limited timeframe.
The pen testers work closely with your internal team to identify vulnerabilities and provide remediation guidance.
Common Types of Penetration Tests:
External Network Penetration Test
Internal Network Penetration Test
API Penetration Test
Web Application Penetration Test
While effective in identifying technical flaws, penetration testing does not evaluate your organisation’s real-time threat detection and response capabilities. That’s where red team testing comes in.
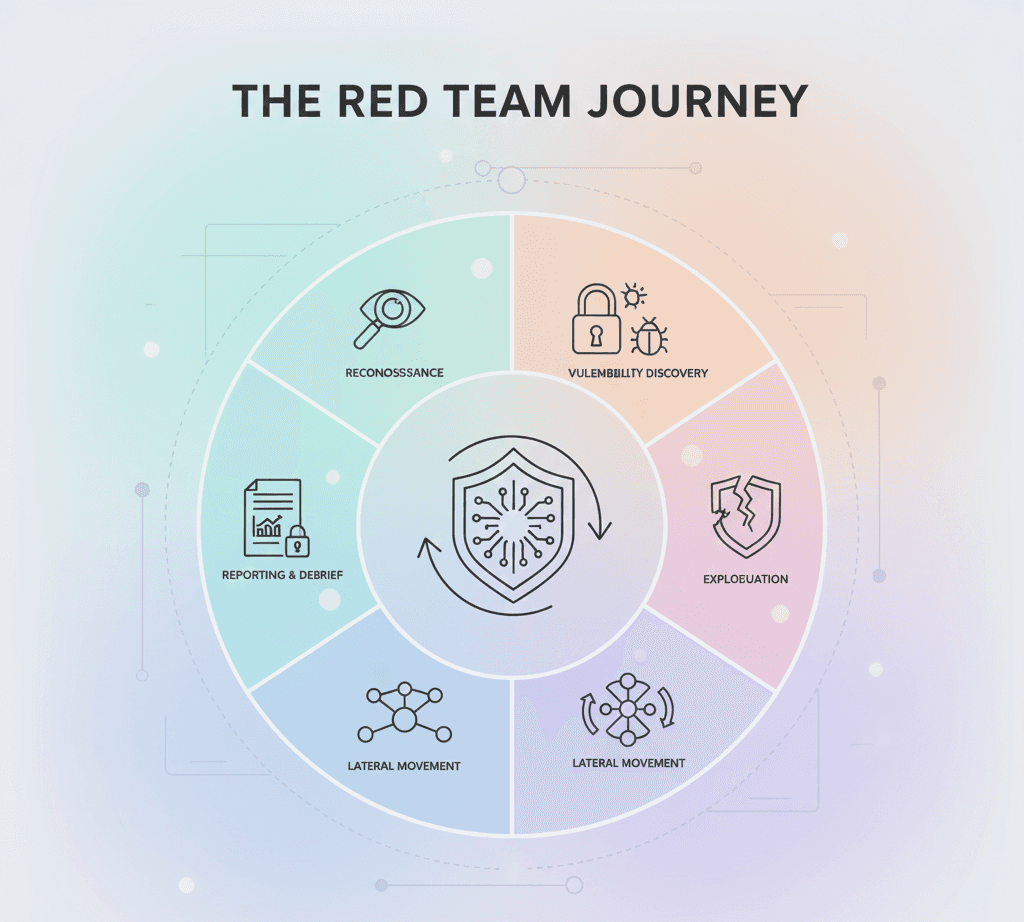
What is Red Teaming?
Red team assessments go beyond identifying technical vulnerabilities. Instead, red team testing simulates a real-world, covert attack to evaluate your organisation’s overall security posture, including:
Technical defenses
Human elements (like social engineering resistance)
Physical security
Incident response effectiveness
In this assessment, a red team cyber security unit attempts to achieve a predefined objective (e.g., gaining access to sensitive data) using any available method, including phishing, exploiting system misconfigurations, or even tailgating into a secure building.
Unlike pen testing, your security team (the blue team) is not informed about the red team operation—making it a more realistic and holistic exercise.
When Should You Choose Pen Testing or Red Teaming?
Choose Penetration Testing If:
Your organisation is new to cybersecurity evaluations.
You need to meet compliance requirements (e.g., PCI DSS, SOC 2, ISO 27001).
You have budget or time constraints and need faster results.
You want to focus on technical controls and remediation planning.
Choose Red Teaming If:
You have a mature cybersecurity program and want to validate its effectiveness.
You need to test how your security team responds to live threats.
You're seeking a realistic simulation of a cyberattack from start to finish.
You’re pursuing FedRAMP ATO, as red team testing is now required under CA-8(2) of FedRAMP Rev. 5.
Final Thoughts: Which Approach is Best for You?
Both penetration testing and red teaming offer tremendous value—but they serve different purposes:
Red penetration testing is ideal for identifying and fixing technical weaknesses quickly.
Red team testing gives you a complete picture of how your entire organisation can detect, respond to, and recover from real-world cyberattacks.
At Accorp, we recommend organisations begin with penetration testing to understand and remediate vulnerabilities. As your security maturity grows, red team cyber security becomes a strategic next step for testing your defences against advanced threats.
Ready to Strengthen Your Security?
If you're considering penetration testing or red team assessments, Accorp’s cybersecurity experts are here to help. We’ll guide you through the best approach for your organisation and provide actionable insights to protect your business.